Ever tried to explain why a website suddenly crawls like a snail after a fresh data dump?
Or spent an entire afternoon watching login attempts bounce back with “invalid credentials” even though you just typed the right password?
If you’ve ever stared at a console log and thought, “What the heck did I break?” you’re not alone. The 3‑1 milestone—database indexing and authentication—is that sweet spot where performance meets security, and getting it right can mean the difference between a smooth launch and a frantic bug‑hunt.
No fluff here — just what actually works.
What Is the 3‑1 Milestone: Database Indexing and Authentication
In plain English, the 3‑1 milestone is the point in a project where you lock down two core pieces:
- Database indexing – the way you tell the database how to find rows fast.
- Authentication – the process that decides who gets in and who stays out.
Think of it like a library. Indexes are the card catalog that point you to the right shelf instantly, while authentication is the library card that proves you belong there. Without a good catalog, you’ll wander aisles forever. Without a card, anyone can walk out with the rare first‑edition The details matter here..
Most teams hit this milestone after the core data model is stable and the first user‑facing screens are wired up. It’s the moment you ask, “Can we find what we need quickly, and can we be sure it’s the right person asking?”
Why It Matters / Why People Care
Speed that users feel
When a query scans an entire table, the delay is palpable. A search that should take 0.Users notice the lag, and the bounce rate spikes. 1 seconds can balloon to 2 seconds—or worse, time out. In practice, a well‑indexed table can shave milliseconds off every request, and those milliseconds add up to a smoother experience The details matter here..
Not obvious, but once you see it — you'll see it everywhere.
Security that actually works
Authentication isn’t just a login form. A sloppy implementation—plain‑text passwords, predictable salts, or missing rate limiting—opens the door to brute‑force attacks, credential stuffing, and data breaches. It’s the gatekeeper that protects personal data, financial info, or anything else you wouldn’t want strangers poking around. Real talk: the fallout from a compromised login system far outweighs the effort of doing it right the first time.
Compliance and trust
Regulations like GDPR, HIPAA, or PCI‑DSS explicitly demand strong authentication and audit‑ready data access. Which means miss a step, and you could be looking at hefty fines or a PR nightmare. The short version is: get indexing and authentication solid early, and you’ll dodge a lot of headaches later.
How It Works (or How to Do It)
Below is the play‑by‑play of what you need to set up for a dependable 3‑1 milestone. I’ll walk through the concepts, then drop in concrete steps you can copy‑paste into your own project.
### Understanding Index Types
| Index | When to Use | Gotchas |
|---|---|---|
| B‑Tree | Most lookups, range queries, ORDER BY | Over‑indexing can hurt writes |
| Hash | Equality checks on exact matches | No range support |
| GiST / SP‑GiST | Full‑text search, geometric data | More complex to maintain |
| BRIN | Very large tables with naturally ordered data | Only works if data is clustered |
The rule of thumb: start with a B‑Tree on every column you filter or sort by, then profile. If you’re dealing with massive logs that are always appended, a BRIN can be a lifesaver Worth keeping that in mind..
### Choosing the Right Columns
- Primary keys are automatically indexed—don’t duplicate them.
- Foreign keys usually need an index if you join on them often.
- Search fields (e.g.,
email,username) get a unique index if the value must be distinct. - Composite indexes—when you frequently filter on two columns together, combine them in the order they appear in the query.
Pro tip: Look at your slow‑query log. The first column in the WHERE clause that isn’t covered by an index is your prime suspect.
### Creating and Maintaining Indexes
-- Simple single‑column index
CREATE INDEX idx_users_email ON users (email);
-- Composite index for (status, created_at)
CREATE INDEX idx_orders_status_date ON orders (status, created_at DESC);
-- Partial index for active users only
CREATE INDEX idx_active_users ON users (last_login) WHERE active = true;
Remember to ANALYZE after big data loads so the planner knows the new distribution.
ANALYZE;
### Authentication Basics
There are three pillars:
- Password handling – hashing, salting, peppering.
- Session management – tokens, cookies, expiration.
- Access control – roles, permissions, scopes.
Password Hashing
Never store raw passwords. Use a purpose‑built algorithm like bcrypt, argon2, or scrypt. They’re deliberately slow, making brute‑force attacks expensive It's one of those things that adds up..
# Example with bcrypt in Python
import bcrypt
def hash_password(plain):
salt = bcrypt.gensalt(rounds=12) # 12 is a good balance
return bcrypt.hashpw(plain.
def verify_password(plain, hashed):
return bcrypt.checkpw(plain.encode('utf-8'), hashed)
Why not SHA‑256? Because it’s fast, which is exactly what attackers want.
Token‑Based Sessions
Stateless JWTs are popular, but they come with pitfalls. If you need revocation, a server‑side store (Redis, DB) is safer The details matter here..
// Node/Express example using jsonwebtoken
const jwt = require('jsonwebtoken');
const secret = process.env.JWT_SECRET;
function issueToken(userId) {
return jwt.sign({ sub: userId }, secret, { expiresIn: '1h' });
}
Set the HttpOnly and Secure flags on cookies, and consider SameSite=Strict unless you have a legit cross‑site need.
Role‑Based Access Control (RBAC)
Define roles (admin, editor, viewer) and map permissions (read:reports, write:posts). Keep the mapping in a separate table so you can change permissions without touching code.
CREATE TABLE roles (
id SERIAL PRIMARY KEY,
name TEXT UNIQUE NOT NULL
);
CREATE TABLE role_permissions (
role_id INT REFERENCES roles(id),
permission TEXT NOT NULL,
PRIMARY KEY (role_id, permission)
);
When a request comes in, pull the user’s role, check the needed permission, and reject if it’s missing.
### Putting It All Together
- Audit your schema. List every column used in
WHERE,JOIN,ORDER BY. - Add indexes based on the audit, starting with the most frequent queries.
- Run
EXPLAIN ANALYZEon those queries to verify the planner uses the new indexes. - Implement password hashing with a modern algorithm, store only the hash.
- Choose a session strategy—JWT for microservices, server‑side store for revocation.
- Set up RBAC tables, seed default roles, and sprinkle middleware checks throughout your API.
- Load‑test both read (search) and write (login) paths. Watch for index contention or lock‑time spikes.
- Monitor—enable slow‑query logs, failed‑login alerts, and token expiration metrics.
Common Mistakes / What Most People Get Wrong
Over‑indexing
Newbies love to “just index everything.On the flip side, write operations become sluggish, and the database can spend more time maintaining indexes than serving queries. ” The result? The sweet spot is usually 1‑2 indexes per table for a modest app.
Ignoring Index Selectivity
An index on a column with only a few distinct values (e.g., a status column with “active/inactive”) often doesn’t help. Plus, the planner may still opt for a sequential scan. Use partial indexes or combine with another column to improve selectivity Practical, not theoretical..
Storing Passwords in Plain Text
I know it sounds obvious, but I still see this in early‑stage startups. A single breach can expose every user’s password—not just on your site, but on any other service where they reused it. Hash, salt, and pepper, then breathe easy.
Relying Solely on Client‑Side Validation
If you only check password strength in JavaScript, a malicious actor can bypass it with a crafted request. Validation must be enforced server‑side as well Which is the point..
Forgetting Token Revocation
JWTs are great until a user logs out or a token is compromised. Without a revocation list (or short expiration + refresh tokens), the token lives until it expires—potentially days.
Hard‑Coding Secrets
Embedding salts, pepper, or JWT secrets in source code is a recipe for disaster. Use environment variables or a secret manager. Rotate them regularly.
Practical Tips / What Actually Works
- Start with a query audit. Pull the top 10 slowest queries from your logs, and index those first.
- Use
EXPLAIN (BUFFERS)to see if the index actually reduces disk reads. - Batch index creation during low‑traffic windows;
CONCURRENTLYin PostgreSQL avoids table locks. - Adopt a password‑policy library (e.g.,
zxcvbn) to give users feedback without reinventing the wheel. - Implement rate limiting on login endpoints (e.g., 5 attempts per IP per 10 minutes).
- Store a “pepper” in a separate secure location (like a vault) and combine it with the user’s salt before hashing.
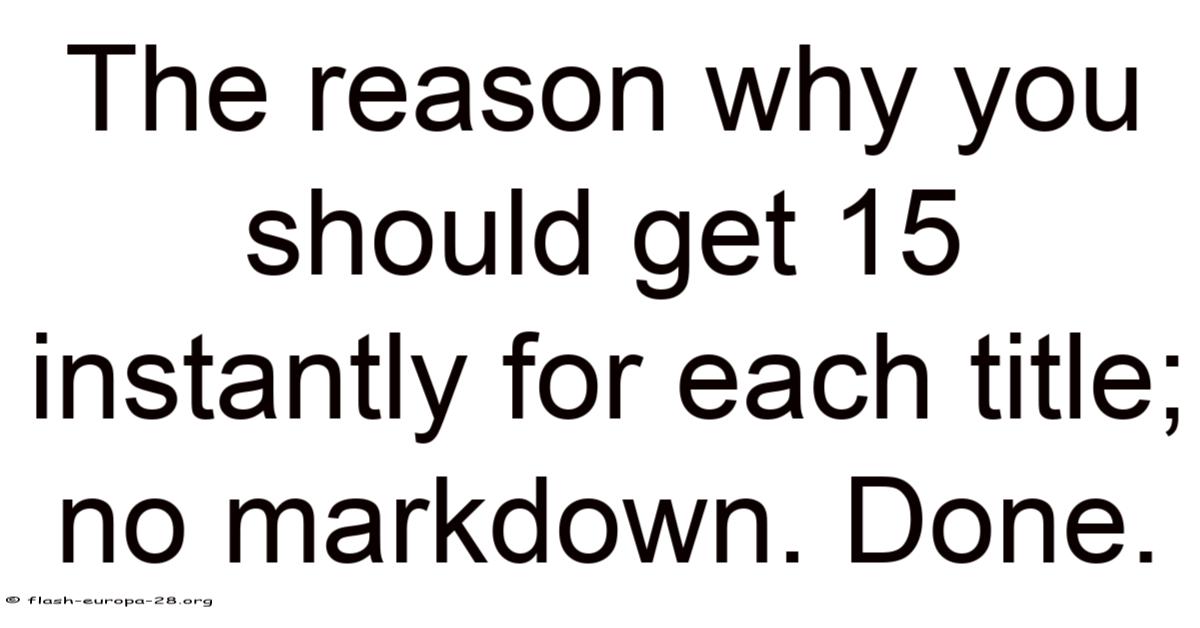
- Prefer short‑lived access tokens (15‑30 minutes) and refresh tokens with revocation support.
- Log authentication events (success, failure, lockout) with timestamps and IPs—great for forensic analysis.
- Run a periodic “index health” script that drops unused indexes (
pg_stat_user_indexescan help) and rebuilds bloated ones. - Automate tests for both performance (benchmark queries) and security (attempt login with wrong passwords, expired tokens).
FAQ
Q: How many indexes is too many?
A: There’s no hard limit, but if write latency spikes by more than 20 % after adding an index, you’ve probably gone too far. Aim for the minimal set that covers your hot paths.
Q: Should I use bcrypt or argon2?
A: Argon2 is the newer, memory‑hard algorithm and is considered the gold standard. If your language ecosystem has solid support, go with Argon2; otherwise bcrypt with a cost factor of 12 is still safe Practical, not theoretical..
Q: Do I need HTTPS for authentication?
A: Absolutely. Without TLS, credentials travel in clear text and can be sniffed. Even internal APIs should be encrypted Practical, not theoretical..
Q: Can I skip indexing on foreign keys?
A: Not advisable. Joins on foreign keys without indexes will force full table scans, killing performance on even modest datasets.
Q: How often should I rotate JWT secrets?
A: Every 30‑90 days is a good practice. Keep the old secret around briefly to validate existing tokens during the transition That alone is useful..
That’s the long and short of the 3‑1 milestone. Nail the indexes, lock down authentication, and you’ll see faster pages, fewer security alerts, and a happier dev team.
Now go ahead—run that EXPLAIN, hash a password, and watch your app finally feel fast and safe. Happy coding!
Monitoring & Observability
- Metrics Dashboard – Export key performance indicators (query latency, CPU/IO utilization, authentication success/failure ratios) to a time‑series platform such as Prometheus or Grafana. Alert when latency exceeds a defined threshold or when the failure rate spikes.
- Structured Logging – Adopt JSON‑formatted logs that include request IDs, user IDs (when available), and correlation tags. This makes it trivial to trace a problematic request across services.
- Distributed Tracing – Integrate OpenTelemetry or a compatible tracer to visualize request flows from the API gateway through the database layer. Spotting a bottleneck becomes a matter of a single click.
CI/CD Integration
- Automated Index Validation – Add a step in your pipeline that runs
EXPLAIN (ANALYZE, BUFFERS)against a representative workload. Fail the build if the estimated cost rises beyond a configurable margin. - Security Scans – Run static analysis tools (e.g., bandit for Python, owasp‑dependency‑check) and dynamic tests that attempt credential stuffing or token replay attacks. Block merges that introduce new vulnerabilities.
- Infrastructure as Code – Keep all configuration, including secret references, in version‑controlled files. Apply changes through pull requests so that any rotation or removal of a secret is auditable.
Scalability & Architecture
- Read Replicas – For workloads dominated by reporting or heavy read traffic, offload queries to one or more read replicas. This reduces pressure on the primary instance and mitigates contention on write‑heavy indexes.
- Connection Pooling – Use a pooler such as PgBouncer or HikariCP to limit the number of concurrent database connections and to recycle idle sockets, preventing resource exhaustion under load.
- Caching Layer – Introduce an in‑memory cache (Redis, Memcached) for frequently accessed, non‑changing data. Set appropriate TTLs and invalidate entries when the underlying source changes to avoid stale reads.
Disaster Recovery
- Point‑In‑Time Backups – Configure continuous WAL archiving for PostgreSQL (or equivalent for your RDBMS) so you can restore to any moment within the retention window. Test restores quarterly.
- Secret Rotation Procedure – Document a step‑by‑step process for rotating database credentials, API keys, and JWT signing secrets. Automate the update of references in your configuration management system to avoid manual errors.
- Failover Testing – Simulate node failures and verify that the system reroutes traffic to the standby instance without data loss or service interruption.
Final Checklist
- Indexes – Verify that every hot query has a supporting index, and that unused indexes have been pruned.
- Authentication – Confirm that passwords are hashed with Argon2 (or a comparable algorithm), that pepper values are stored separately, and that token lifetimes are short with revocation support.
- Observability – Ensure metrics, logs, and traces are flowing to your monitoring stack and that alerts are actionable.
- CI/CD – Validate that every pull request passes performance, security, and integration tests before merging.
- Recovery – Run a full backup‑restore drill and confirm that secret rotation can be executed without downtime.
Conclusion
By systematically addressing performance at the query level, fortifying authentication mechanisms, and embedding observability, testing, and recovery into the development lifecycle, you create a resilient foundation for any application. The practices outlined above are not isolated tasks but interlocking components that reinforce each other: a well‑indexed database reduces load on authentication services, while dependable logging and monitoring make it possible to detect and remediate issues before they affect users It's one of those things that adds up..
Implement the checklist, iterate based on real‑world data, and you’ll see tangible
Ensuring high availability and reliability in your PostgreSQL environment requires a multi‑layered strategy. By deploying read replicas, you distribute the workload effectively, easing pressure on the primary instance and reducing contention during peak operations. Pairing this with intelligent connection pooling and an in‑memory cache further optimizes performance, especially for read‑heavy workloads.
Equally important is a solid disaster recovery plan. Continuous backups of write‑aware archives, disciplined secret rotation, and regular failover testing form a safety net that protects against data loss and service disruption. These measures, when integrated thoughtfully, create a resilient architecture capable of withstanding unexpected challenges.
As you refine your setup, remember that vigilance is key. Regularly review indexes, enforce strong authentication, and keep observability tools active to maintain a healthy, responsive system. Following this comprehensive approach not only strengthens performance but also builds confidence in your application’s stability.
Conclude with the understanding that a well‑managed PostgreSQL stack, supported by these practices, stands as a solid pillar for your digital infrastructure.